Google has fallen victim to its own ad platform, allowing threat actors to create fake Google Authenticator ads that push the DeerStealer information-stealing malware.
In a new malvertising campaign found by Malwarebytes, threat actors created ads that display an advertisement for Google Authenticator when users search for the software in Google search.
What makes the ad more convincing is that it shows ‘google.com’ and “https://www.google.com” as the click URL, which clearly should not be allowed when a third party creates the advertisement.
We have seen this very effective URL cloaking strategy in past malvertising campaigns, including for KeePass, Arc browser, YouTube, and Amazon. Still, Google continues to fail to detect when these imposter ads are created.
Malwarebytes noted that the advertiser’s identity is verified by Google, showing another weakness in the ad platform that threat actors abuse.
When the download is executed, it will launch the DeerStealer information-stealing malware, which steals credentials, cookies, and other information stored in your web browser.
Users looking to download software are recommended to avoid clicking on promoted results on Google Search, use an ad blocker, or bookmark the URLs of software projects they typically use.
Before downloading a file, ensure that the URL you’re on corresponds to the project’s official domain. Also, always scan downloaded files with an up-to-date AV tool before executing.


They also have some trackers I think. Try SearxNG.
Urgh I hate apple. Can’t choose something else but these default options. And I have to use the safari browser because it is the only one that has the accomodations for my disability I need.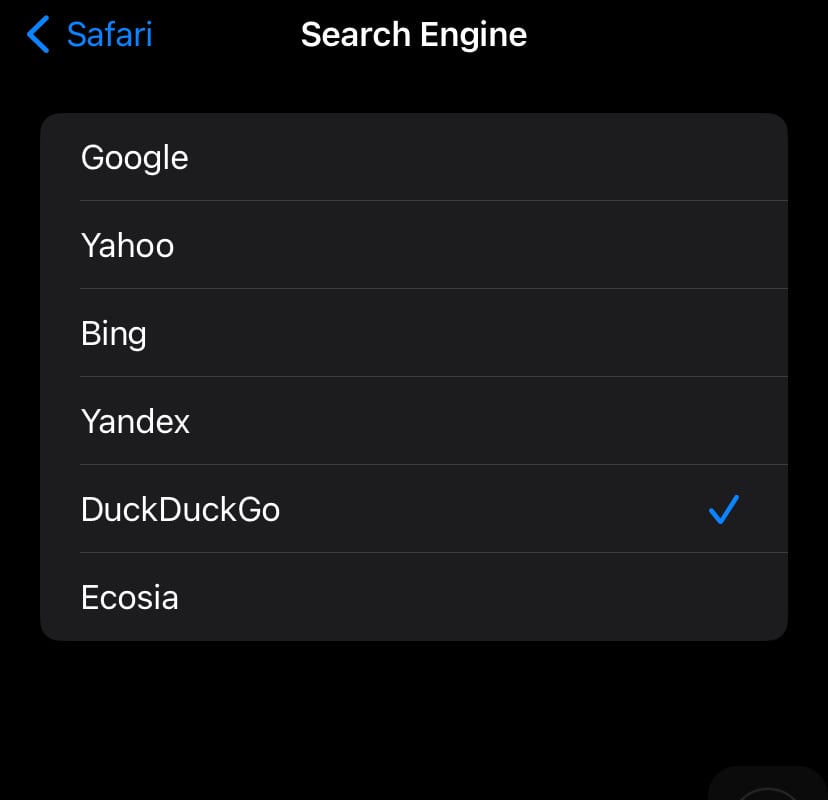
(replying from my alt cuz image hosting is down on blahaj.zone)
You did this to yourself when you bought an Apple device
Android doesnt have the accessibility things I need at all 🤷 didnt have much of a choice.
I’m sorry you have to deal with that. And I’m sorry you don’t have a choice
They can just install another browser…
Actually I found a way to bypass this using the “hyperweb” extension, if anyone needs in future